Table of Contents
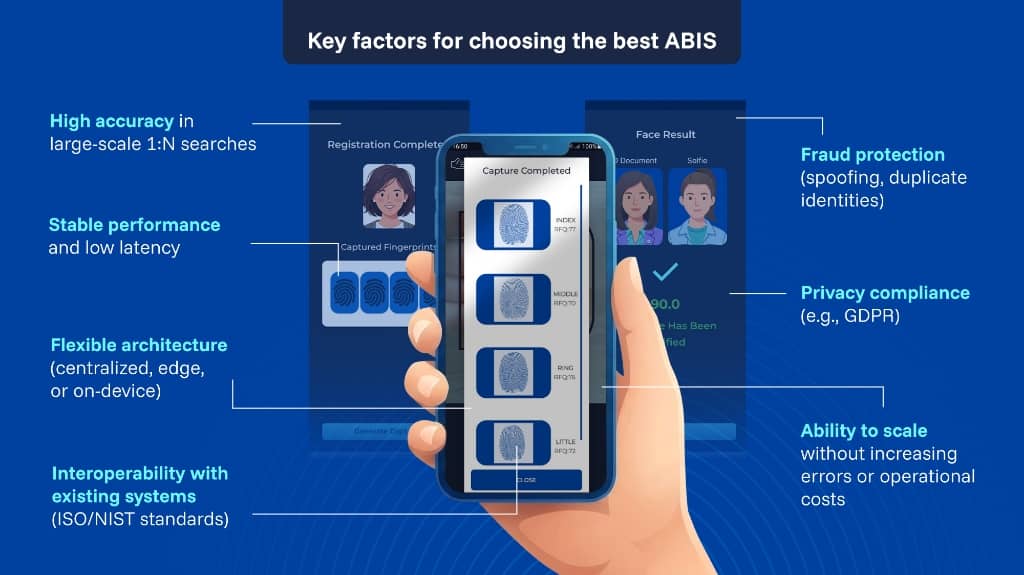
ToggleThe “best ABIS” is the one that makes identity decisions dependable when volume explodes: national registries, border systems, and digital onboarding funnels that must screen users in seconds. An automated biometric identification system supports both verification (1:1) and identification (1:N) by storing and matching biometric data at operational speed.
Deepfakes are becoming more sophisticated, increasing the risk of fraud and identity manipulation in digital environments. Download our 10-step guide to learn how to detect threats early and protect your organization with proven best practices.
What is ABIS?
Government and defense programs describe ABIS in consistent terms: a system that ingests biometric submissions, stores records, searches for matches, and supports high transaction rates and watchlist-style workflows.
For decision makers, that means the ABIS is not “just a matcher.” It is biometric identification system software that must be governed like critical infrastructure: performance you can measure, failure modes you can recover from, and evidence you can defend in audits.

ABIS Biometrics: scaling 1:N identification and throughput
1:N is where scale punishes weak design. Guidance on large-scale identity systems explains that identification error behavior depends on database size and that growing N can increase false candidates, driving manual adjudication costs unless quality controls and operating thresholds are engineered up front.
Operational ABIS deployments frequently manage this risk by returning a shortlist (not a single “yes/no”), with policies defining when expert review is required. Estonia’s ABIS documentation describes 1:1 verification and “one-on-multiple” identification that returns similar candidates for expert decisioning.
Independent testing reduces procurement risk. NIST runs evaluations such as FRVT, including 1:N identification testing, enabling buyers to compare accuracy trade-offs across operating points using consistent datasets and protocols.
Get a tailored demo of our contactless biometric platform and see how it fits your specific use case.
Architecture and cost: centralized, edge, and on-device
ABIS architecture is a business lever. Centralized matching supports large watchlists and national registries; edge and mobile capabilities can reduce latency, avoid network bottlenecks, and improve continuity during outages or low-connectivity operations. ISO/IEC guidance on mobile biometrics emphasizes local biometric identity verification and end-to-end performance testing for full systems embedded in mobile devices.
The hybrid pattern that is becoming common
Many large programs land on hybrid designs: on-device capture validation and privacy-preserving pre-processing, paired with centralized 1:N matching when needed. Identy.io is one example of a large-scale biometric identification platform designed for both 1:1 verification and 1:N identification, and it describes an on-device, privacy-first architecture. Identy.io is also listed in the FIDO Alliance member directory; the alliance states that FIDO standards use standard public-key cryptography techniques to provide phishing-resistant authentication.
Standards, interoperability, and measurable accuracy
Interoperability determines total cost of ownership. When ABIS must connect to legacy registries, border systems, and KYC stacks, standards reduce friction and re-enrollment risk. International Organization for Standardization standards define how to test biometric performance and throughput (ISO/IEC 19795-1), how to exchange biometric data (ISO/IEC 19794 series), and how to package biometric information records through CBEFF (ISO/IEC 19785-1). NIST also publishes background on CBEFF descriptive data, designed to reveal record format and attributes without exposing the biometric data itself.
Security, fraud prevention, and privacy readiness
A “best ABIS” assumes adversarial conditions: spoofing at capture, injection into enrollment flows, and attempts to create duplicate identities. ISO/IEC 30107-1 provides a framework for presentation attack detection, and NIST biometrics collection guidance addresses controls against impersonation and spoofing.
Privacy is non-negotiable. Under European Union GDPR, biometric data used for unique identification is special-category personal data with strict conditions for processing, and NIST guidance stresses consent and privacy controls around biometric collection and use.
Choosing the best ABIS is choosing what you will scale: exceptions, or certainty. Prioritize systems that keep latency predictable at peak volume, publish measurable performance, and use standards-based interoperability so you are not forced into costly re-enrollment when systems evolve.
Get a tailored demo of our contactless biometric platform and see how it fits your specific use case.
Bibliography
-
- World Bank. A Primer on Biometrics for ID Systems.
- NIST. Face Recognition Vendor Test (FRVT). https://www.nist.gov/programs-projects/face-recognition-vendor-test-frvt
- ISO/IEC 19795-1 and ISO/IEC 19794 series (performance testing; data interchange formats). https://www.iso.org/standard/73515.html
- Regulation (EU) 2016/679 (GDPR), Article 9. https://eur-lex.europa.eu/legal-content/EN/TXT/HTML/?uri=CELEX%3A02016R0679-20160504