Table of Contents
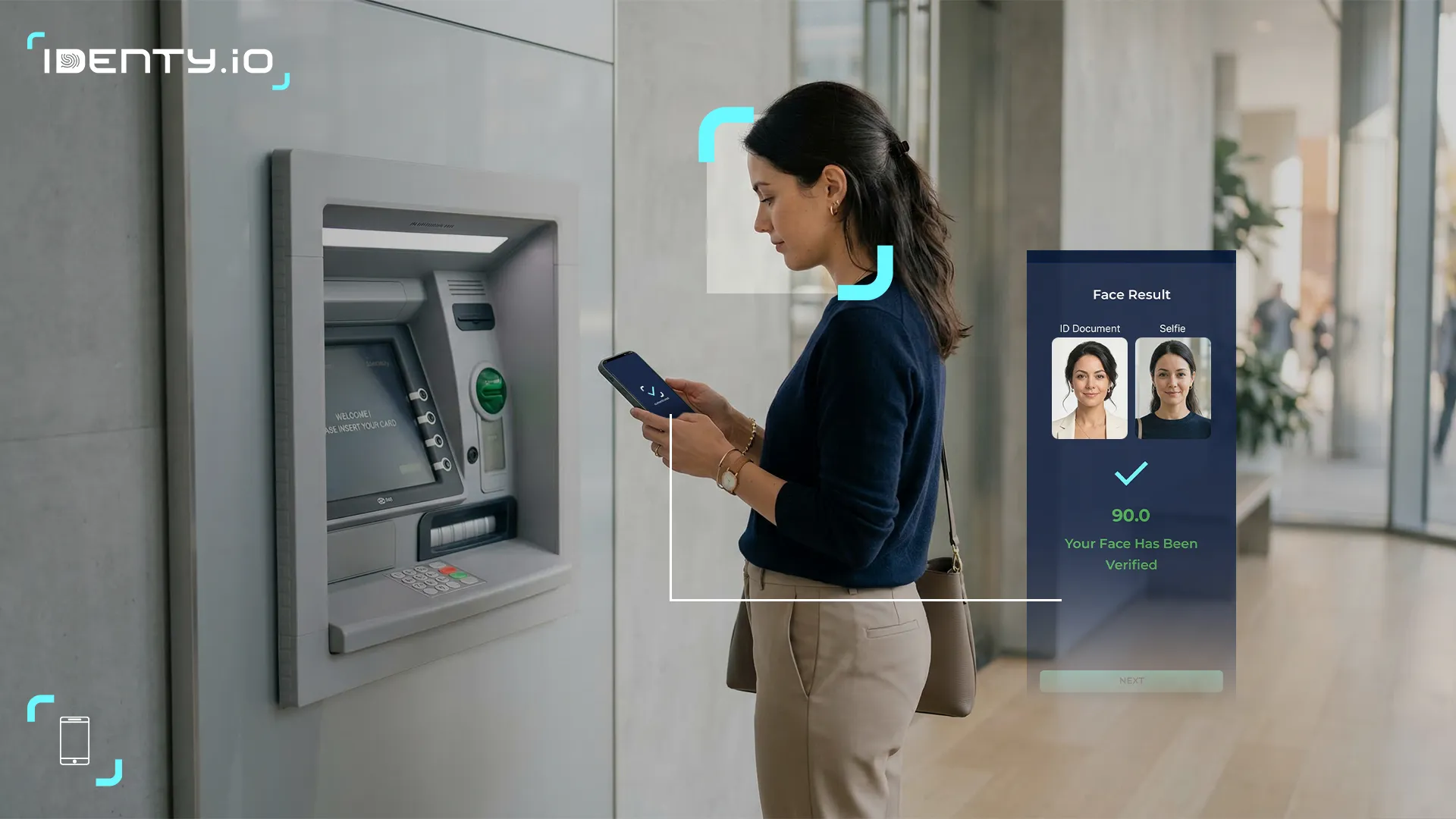
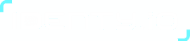
ToggleOn-device biometric authentication, using a customer’s own smartphone or tablet to verify identity via fingerprint biometric, facial biometric, or other biometric sensors, has emerged as a leading strategy for securing mobile banking. Unlike traditional OTP or server-side systems, on-device biometrics keeps sensitive templates on the user’s device, reducing fraud risk and strengthening privacy. Industry standards (notably FIDO2) and regulatory frameworks increasingly favor biometric “something you are” factors as part of strong authentication. For finance leaders, this approach lowers business risk from account takeover (eliminating vulnerabilities like SIM‑swap attacks) while enhancing user experience with fast, passwordless logins. It aligns with data-protection laws (e.g. GDPR classifying biometric identifiers as sensitive) and scales efficiently since each device handles its own matching. Solutions like Identy.io’s FIDO-certified on-device platform (which uses a phone’s camera for touchless fingerprint verification) illustrate how banks can deploy strong authentication that is both secure and user-friendly. This article examines how on-device biometrics balances security, trust, compliance, user experience, scalability, and deployment models, concluding that it offers a strategic advantage in mobile banking.
Deepfakes are becoming more sophisticated, increasing the risk of fraud and identity manipulation in digital environments. Download our 10-step guide to learn how to detect threats early and protect your organization with proven best practices.
Business risks and security On-Device biometric authentication
Mobile banking faces escalating fraud threats (phishing, account takeovers, identity theft). Legacy methods like SMS OTP or passwords are increasingly inadequate: OTP messages can be intercepted or hijacked (via SIM swap or SS7 attacks). On-device biometrics (often implemented via FIDO2 standards) eliminate these vulnerabilities by tying authentication to the user’s own device and biometrics. A recent FIDO Alliance report notes that device-bound authentication “eliminates the need for SMS OTPs”, thereby thwarting SIM‑swap and password-replay attacks. Because passive liveness detection and biometric matching occur entirely on-device, inside the device’s secure enclave (Apple Secure Enclave or Android TrustZone), there is no central repository of biometric data for attackers to breach. Industry adoption reflects this strength: major banks and payment networks (e.g. Visa, Mastercard, Bank of America) have chosen FIDO-based on-device biometrics to bolster security. In practice, banks that add fingerprint or face login see dramatic fraud reductions. For example, Banco Popular Dominicano deployed Identy.io’s on-device fingerprint and face biometrics in its mobile app, delivering secure authentication with measurable reductions in account-takeover incidents.. By reducing reliance on shared secrets and SMS channels, on-device biometrics cuts the chief pathways fraudsters exploit, thereby lowering business risk substantially.
Digital trust and UX
Strong authentication must earn customers’ trust without adding friction. On-device biometrics delivers both: it is more convenient than passwords/PINs and perceived as more secure. Consumer surveys confirm rising trust in biometrics, over half of users now authenticate with biometrics daily, and many cite speed and convenience as key benefits. Remarkably, one study found that despite privacy concerns, 91% of people still completed transactions when prompted for biometric authentication. Customers equate biometric login with leading-edge digital services, boosting a bank’s brand trust. However, trust also depends on transparency: users expect strict data policies. On-device processing addresses this by never transmitting raw biometric data off the device. For instance, Identy.io’s platform (a FIDO Alliance member) performs all matching via the phone’s camera and cryptographically secures templates locally, which builds user confidence that their sensitive biometric templates are not stored in any cloud database. In sum, on-device biometrics enhances the customer experience with one-tap logins and helps banks build digital trust by showing strong, privacy-preserving security.
Get a tailored demo of our contactless biometric platform and see how it fits your specific use case.
Regulatory compliance and standards
Regulators worldwide are demanding stronger authentication, and biometrics are a favored solution. In the EU, PSD2’s Strong Customer Authentication (SCA) rules require two-factor auth for payments (something you know, have, or are). Biometric factors naturally satisfy the “something you are” element while remaining user-friendly. The European Commission explicitly noted that SCA “makes it easier and safer for consumers” to pay online.
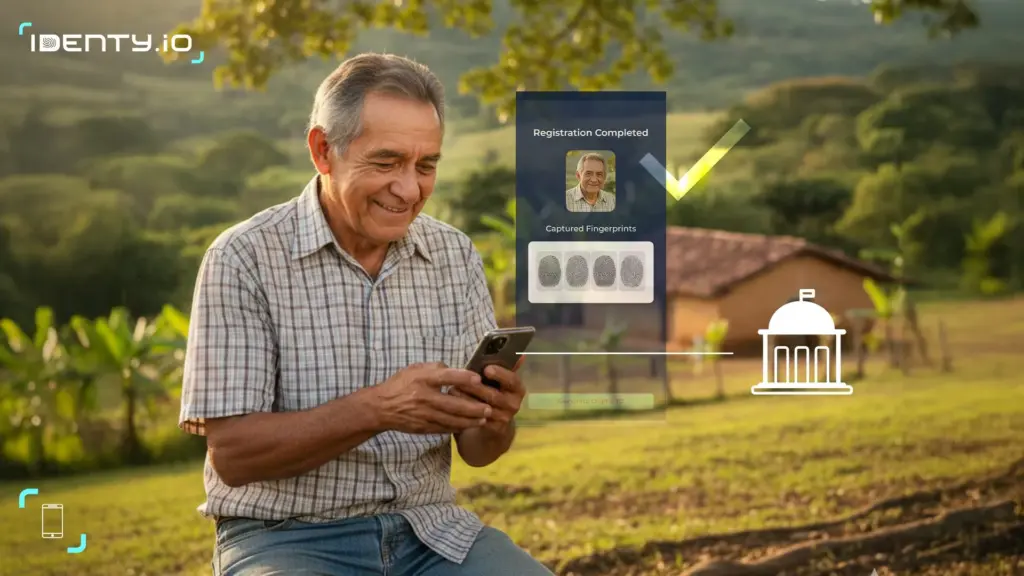
Similarly, the UK’s FCA has endorsed biometric and behavioral factors to combat fraud under its PSD2-aligned guidance. In India, the central bank’s 2020 Digital Payment Controls mandate robust security in mobile banking; a FIDO Alliance white paper cites FIDO-based on-device biometrics as an ideal way to meet these RBI requirements while enhancing UX. Moreover, data-privacy laws treat biometric identifiers as sensitive.
For example, EU GDPR expressly classifies biometric data used for identification as a “special category” requiring consent and protection. On-device biometrics inherently helps compliance: because templates never leave the user’s device, banks avoid many cross-border data concerns and reduce scope of sensitive data handling. Leading standards bodies reflect this trend.
The FIDO Alliance (of which Identy.io is a member) has over 900 certified devices supporting passwordless biometric login, and major OS vendors (Apple, Google, Microsoft) have built native support. In practice, adopting FIDO-certified, on-device mechanisms aligns banking apps with both security regulations and privacy laws, and helps meet anti-fraud (KYC/AML) mandates by providing strong, verifiable user identity proof without overexposing personal data.
Scalability and deployment models
On-device authentication scales naturally because each mobile device does its own processing. In practice, the biometric matching and cryptographic proofs occur on the user’s smartphone, offloading work from central servers. This distributed model can support millions of users without large server farms. In contrast, server-side biometrics (often “Biometrics-as-a-Service”) requires every template and matching request to travel over the network, creating latency and a central point of failure. Goode Intelligence (a research firm) notes that banks will often choose the on-device (device-centric) model – where biometric data never leaves the device – to meet privacy/trust needs. Such models leverage built-in secure hardware (Secure Enclave, TrustZone), which also simplifies certification (e.g., FIDO’s multi-factor authenticators).
From an integration standpoint, banks can deploy on-device biometrics via mobile app SDKs and mobile OS APIs. This typically involves a one-time registration of the user’s fingerprint or face (enrolled locally) and subsequently using that to unlock the stored key on-device. Because modern smartphones already include fingerprint readers or cameras, deployment cost is low. Leading financial institutions often roll out biometrics gradually, combining on-device methods with fallbacks (e.g., PIN entry or 2FA) as needed. Over time, as more users adopt it, the load shifts away from legacy auth infrastructure. Identy.io, for example, offers a turnkey solution that turns any mobile camera into a multi-finger fingerprint reader with liveness proof. By contrast, a fully server-based deployment would require maintaining a secure template database and scaling it globally, a far less flexible and potentially slower model.
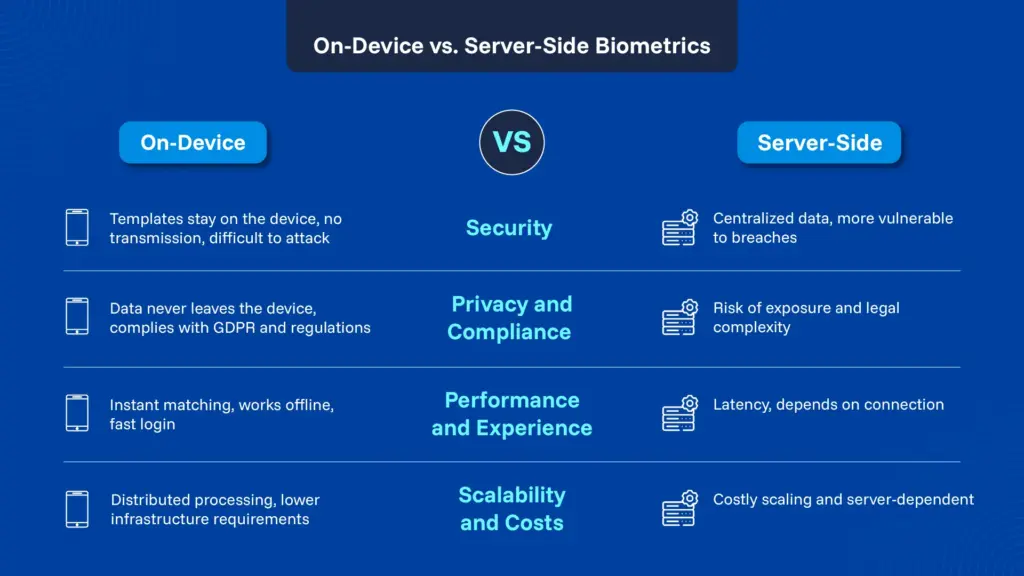
On-Device vs. Server-Side: Comparison
|
Factor |
On-Device Biometrics |
Server-Side Biometrics |
|
Security |
High – Biometric templates remain in the device’s secure enclave; hard for attackers to compromise in transit. No shared secret is sent over networks. |
Moderate – Central storage of templates can be a target; network channels may be intercepted. Attacks on the server or during transmission can compromise security. |
|
Privacy |
Strong – Biometric data never leaves the user’s device, minimizing privacy exposure. Complies better with data-protection laws (e.g. GDPR’s special-category rules ). |
Weaker – Banks or third parties store biometric templates, raising regulatory and user privacy concerns. Data jurisdiction and consent issues are more complex. |
|
Latency |
Low – Matching is done locally on the device, giving near-instant response and no network delay. |
Higher – Each authentication requires a round-trip to server, introducing network latency and dependency on connectivity. |
|
Scalability |
High – Authentication load is distributed across user devices. Minimal additional server-side capacity is needed. |
Variable – As user base grows, servers must scale to handle match requests and storage, incurring infrastructure and maintenance costs. |
|
Compliance |
Favorable – Aligns with “phishing-resistant” MFA trends. Eases compliance since no central biometric database is needed. Many modern regulations and standards (FIDO, PSD2 SCA) explicitly permit or encourage device-based biometrics. |
Challenging – Requires meeting stricter controls for centralized sensitive data. Additional safeguards (encryption, consent management) and audits are needed to satisfy GDPR, PCI, and other rules. |
For fintech and banking leaders, on-device biometric authentication represents a strategic, future-proof investment. It delivers a measurable reduction in fraud risk (by eliminating weak factors like SMS OTP) while elevating customer trust and satisfaction through seamless, intuitive login. Scanning market trends and regulatory signals, it’s clear that strong, passwordless methods, anchored in “something you are”, are moving from optional to essential. Implementing on-device biometrics also prepares organizations for next-generation identity schemes (such as passkeys) and aligns with ecosystem standards. As an illustration, Identy.io’s FIDO-compliant platform leverages touchless fingerprint capture on smartphones, exemplifying how banks can adopt these methods in real-world systems. By choosing on-device biometrics, institutions can achieve strong multi-factor authentication at scale without compromising privacy or user experience. In conclusion, this approach turns security investment into a competitive advantage: it meets regulatory demands (e.g. PSD2 SCA, GDPR), fortifies digital trust, and enables mobile banking to grow securely.
Get a tailored demo of our contactless biometric platform and see how it fits your specific use case.
Bibliography
- FIDO Alliance – FIDO Authentication in Digital Payment Security (white paper).
- Goode Intelligence – Biometrics for Customer-First Banking (white paper).
- Identity Theft Resource Center – Consumer Trust in Biometrics Report.
- European Commission – Strong Customer Authentication requirement of PSD2 (press release).
- European Parliament – GDPR Article 9: Special category data (biometrics).
- FIDO Alliance – Company Profile: Identy.io
- Company Profile: Identy.io