Table of Contents
ToggleAs financial institutions and governments digitize services, identity theft has emerged as a top business risk. Cybercriminals now use AI deepfakes and synthetic identities to bypass traditional safeguards. Robust identity theft protection software must therefore blend advanced detection (dark-web scanning, AI anomaly analysis), passwordless/FIDO-compliant authentication, and strong compliance controls. Leading platforms (for example, Identy.io – a FIDO Alliance member) illustrate how on-device biometrics and passive liveness detection can secure identities without sacrificing user experience. In 2026, organizations should evaluate identity theft protection software on business-impact criteria: minimizing fraud losses, preserving customer trust, ensuring regulatory compliance (KYC/AML, privacy laws), and scaling seamlessly. This article analyzes key features and trends in identity-fraud prevention solutions tailored for fintech, banking and government, focusing on employee- and customer-centric use cases, digital trust, UX, and scalability.
Deepfakes are becoming more sophisticated, increasing the risk of fraud and identity manipulation in digital environments. Download our 10-step guide to learn how to detect threats early and protect your organization with proven best practices.
Rising identity theft risks in finance and government
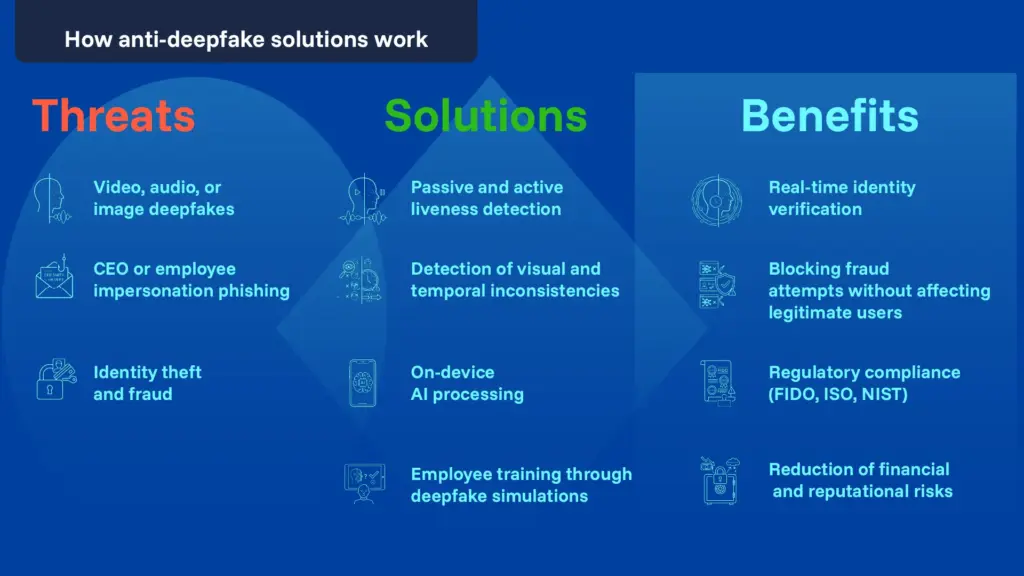
Identity theft has become the fastest-growing financial crime according to the FTC. Regulators warn that criminals now exploit generative AI to create fake IDs, photos and videos to defeat verification checks. For example, a U.S. Treasury alert reports increasing “deepfake media” schemes targeting banks: attackers use AI-generated documents and spoofed biometrics to slip past login and onboarding systems. Biometric fraud stats are alarming: Entrust’s 2026 fraud report finds one in five biometric fraud attempts involved deepfakes. Fraudsters also target high-risk areas (e.g. cryptocurrency) and 24/7 operations, so identity attacks can occur anytime. Even well-intentioned employees pose risks: industry surveys show 62% of insider incidents stem from negligent or compromised users, not malice, and 73% of security teams worry about careless employees handling sensitive data.
Together, these trends underscore that identity fraud is a business-wide concern. A breach or spoofed employee ID can lead to costly financial losses (41% of firms saw $1M–$10M insider-incident losses) and erode customer trust. Governments are responding: the EU’s Digital Identity Wallet regulation (eIDAS 2.0) mandates secure digital IDs to reduce fraud, while U.S. standards (NIST SP800‑63) emphasize usability alongside security. In this climate, identity theft protection software must integrate fraud prevention with strong compliance support and user-friendly authentication to maintain digital trust.
Key features of identity theft protection software
Top identity theft protection software combines multiple layers of monitoring and verification:
- Real-time identity monitoring: Continuous scanning of dark-web databases, credit bureaus, and data broker feeds for exposed PII (SSNs, login credentials, etc.) alerts administrators immediately if employee or customer data is compromised. This rapid alerting (real-time versus batch-data) is critical to “stop or minimize” damage.
- Anomaly and fraud detection: AI-driven analysis of login and transaction patterns can spot unusual activity (e.g. impossible travel, atypical hours) and flag potential account takeovers. Modern solutions often use machine learning to adapt as fraud tactics evolve.
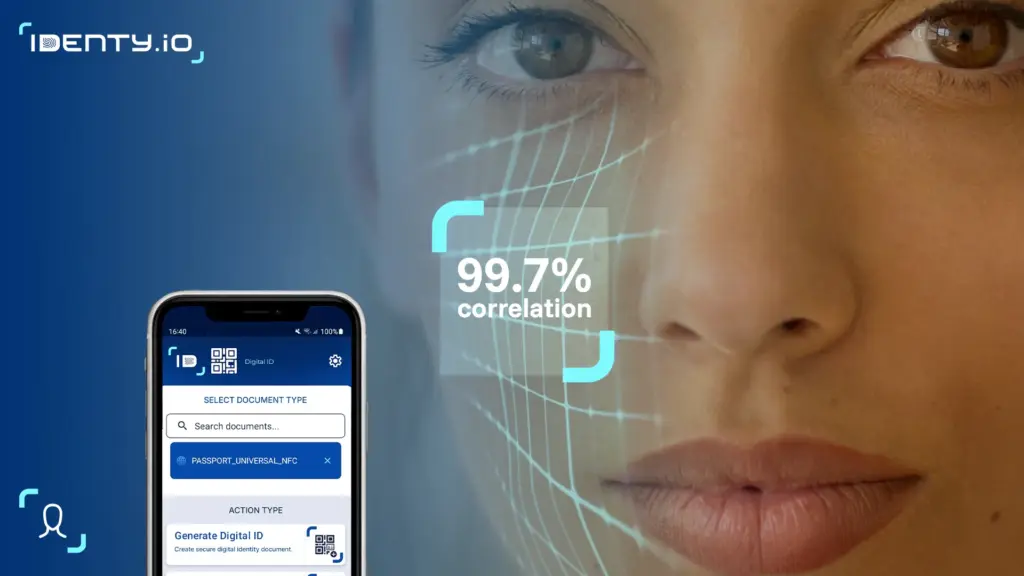
- Multi-factor and biometric authentication: By enforcing strong authentication (biometric, hardware tokens or FIDO passkeys) for employees and customers, solutions make it far harder to impersonate someone. For instance, FIDO-compliant passkeys replace passwords with cryptographic credentials bound to a device, eliminating credential reuse and phishing risks. Users simply unlock with a fingerprint or face scan, streamlining UX. Identy.io performs all biometric matching directly on the user smartphone, no biometric data is ever transmitted to a server. This on-device architecture delivers real-time response, works offline, and is privacy-by-design.
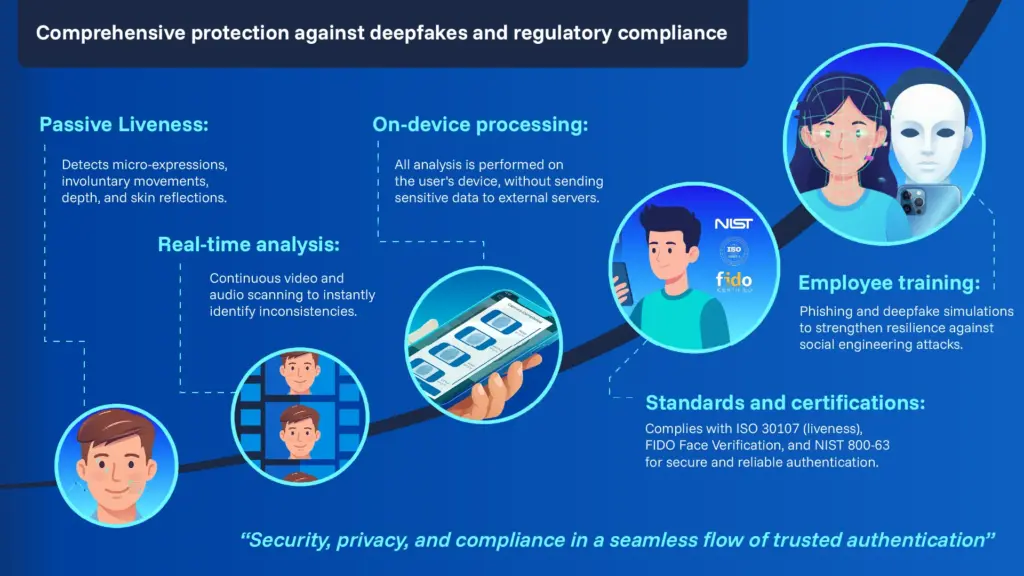
- Passive liveness and anti-spoofing checks: Advanced platforms use passive liveness detection , running silently in the background, with no prompts or user actions required , to verify that the biometric sample comes from a real, live person. AI models analyze skin texture, depth, micro-movements, and lighting cues to detect printed photos, video replays, 3D masks, and AI-generated deepfakes.
- Employee identity protection: Proactive features for staff include identity-monitoring subscriptions or alerts for suspicious employment records (fake W-2s, new tax filings on an employee’s SSN). Some organizations even offer employee identity theft protection software as a benefit, recognizing that personal identity breaches (e.g. a stolen SSN) can become corporate incidents. For example, LinkedIn or HR profile monitoring can prevent imposter accounts on corporate systems.
Incident remediation support: Many solutions bundle recovery services (credit freezes, legal aid) so that if theft occurs, employees and customers get guided, “white glove” remediation. This reduces downtime and reputational damage.
In short, the best anti identity theft software solutions are layered and adaptive, combining backend monitoring with seamless front-end authentication. A tabular overview of feature trade-offs (e.g. usability vs assurance level) can help stakeholders compare options (see footnote suggestion for a chart).
Get a tailored demo of our contactless biometric platform and see how it fits your specific use case.
Biometric authentication and FIDO Standards
Biometrics (fingerprint, face, iris) have become mainstream for biometric identity verification, but they must be implemented securely. International guidance stresses protecting biometric templates with encryption and strict data governance. Identy.io performs all matching on the user smartphone and never stores raw biometric data centrally — a design that satisfies GDPR data minimisation requirements and eliminates the server-side breach risk that plagues cloud-dependent alternatives. This approach limits breach risk while enabling passwordless login.
In enterprise use-cases, replacing passwords with FIDO-based passkeys has clear benefits: “FIDO authentication reduces the risk of phishing and eliminates credential reuse,” while improving speed and ease of access for employees and partners. By using device-bound cryptographic keys or synced passkeys, organizations remove a major attack vector. Crucially, NIST’s 2025 Digital Identity guidelines echo this, urging multi-factor and decoupling from shared secrets for both high-assurance and everyday services. Identy.io’s own suite illustrates this design: it combines on-device biometrics with FIDO-based passkeys, and its passive liveness engine silently detects spoofing and deepfakes in real time, without the user ever being prompted.
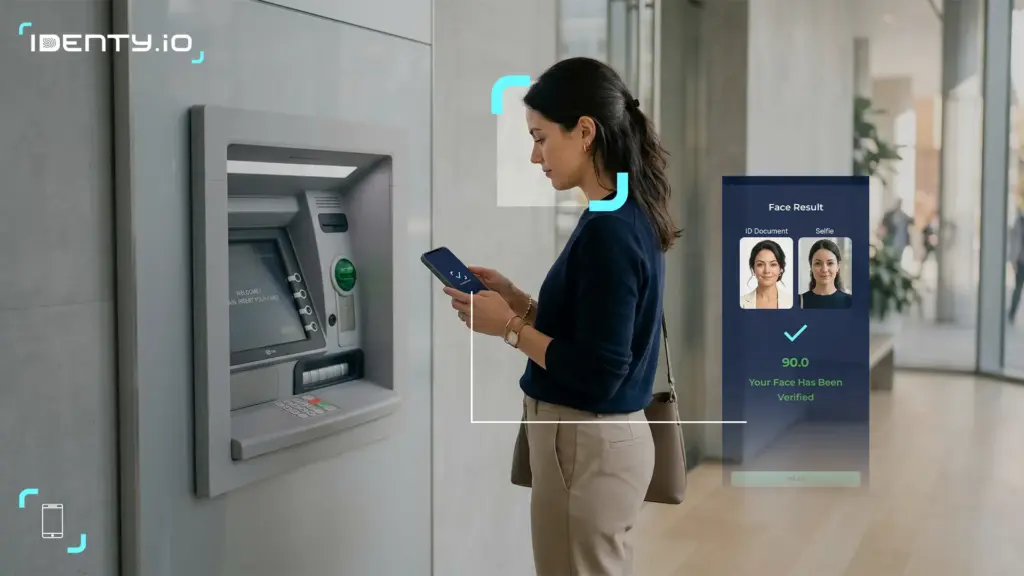
For user experience, biometric/FIDO solutions can be frictionless: logging in or approving a transaction is as simple as a fingerprint scan. Behind the scenes, cryptographic binding and on-device AI continuously validate identity, with sub-second latency even on mid-tier Android devices. This “passkey” model scales across millions of users while sidestepping the password fatigue that often leads to breaches.
Compliance, trust and scalability considerations
Any identity protection platform must align with relevant regulations. In banking and fintech, KYC/AML rules compel strong identity proofing, so the software should enable reliable customer onboarding (automated ID checks, documented audit trails) and ongoing authentication. For government e-services, standards like GDPR and eIDAS/EUDI require data minimization and transparency in identity processing. The EU Digital Identity framework, for instance, mandates digital wallets to ensure fraud “is reduced” through verifiable identity.
Regulators are also demanding resilience against new threats: FinCEN has explicitly alerted institutions about GenAI-facilitated fraud, and NIST now embeds controls for deepfakes in guidance. Best-in-class solutions will offer tools (like AI-driven document verification or biometrics certified against standards) that directly address these concerns. In practice, this means choosing vendors with third-party certifications (e.g. ISO27001, FIDO Compliance) and clear privacy compliance (e.g. encryption, consent management) baked in.
From a strategic viewpoint, deploying identity theft protection software is a long-term investment in digital trust. It can enhance user experience (fast, passwordless access), boost revenue (by reducing fraud-related losses), and strengthen brand reputation. Scalability is key: the chosen system must handle peak loads and large user bases (cloud-native architectures, horizontal scaling, and APIs for integration). Moreover, the provider’s roadmap should match your needs for emerging tech (AI fraud detection, interoperability with new ID schemes, etc.).
By 2026, the best identity theft protection software for enterprise use will be those combining verifiable certifications, on-device processing, and frictionless biometric authentication. Identy.io shows how a passive liveness and FIDO-based architecture can give banks and governments the tools to verify users quickly, while making deepfake and spoofing attacks impractical
Senior leaders should view identity protection not just as a technical control but as a cornerstone of digital trust. A robust solution proactively shields both employee and customer data, preserving productivity and confidence. It also signals to regulators and clients that you take identity security seriously. In practice, organizations might pilot solutions on high-risk workflows (e.g. new account opening or privileged access) and expand as ROI is demonstrated.
In summary, selecting a top-tier identity theft protection suite in 2026 means balancing security efficacy, user experience, and regulatory compliance. With increasing AI threats and stricter ID frameworks, solutions built on passive liveness detection, on-device processing, and proven certifications will lead. Implementing such solutions will help fintechs, banks and government agencies manage fraud risk, enhance digital trust, and scale their operations securely into the future.
Trusted external references: Authoritative sources shaping this domain include the FIDO Alliance (passkey standards), NIST (digital ID guidelines), U.S. agencies (FinCEN, FTC/IdentityTheft.gov), the European Commission (eIDAS/EU Digital Identity regulation), the World Economic Forum (AI and security reports), the World Bank’s ID4D initiative (biometric ID guidance), and specialist media like Biometric Update that track deepfake and identity-fraud trends. These organizations provide up-to-date guidance and research on biometrics, anti-fraud, and identity security.
Get a tailored demo of our contactless biometric platform and see how it fits your specific use case.
Bibliography
-
Biometricupdate.com
-
http://fidoalliance.org/company/Identy.io/
-
https://www.nist.gov/