Table of Contents
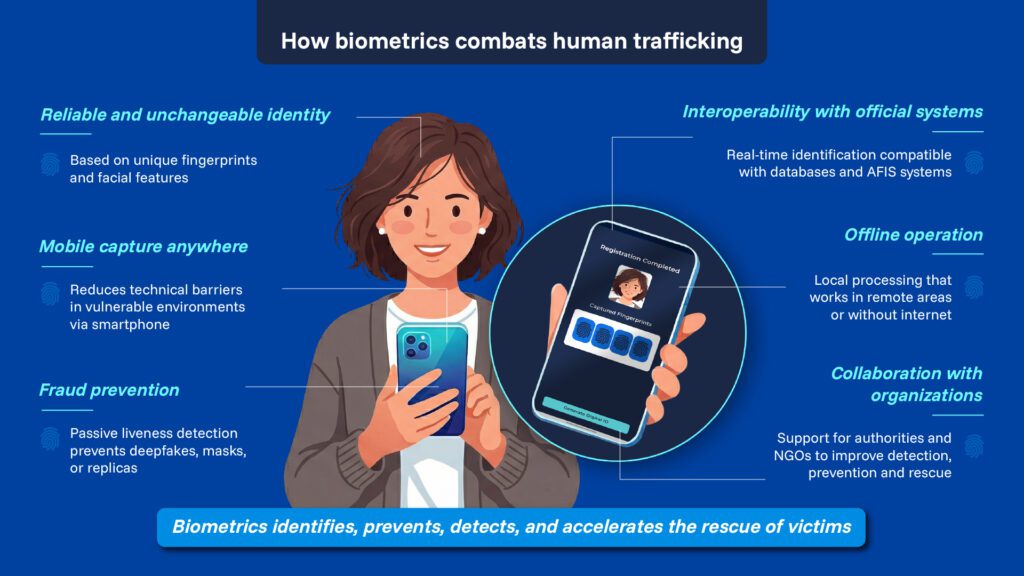
ToggleHuman trafficking continues to be among the most serious and complex human rights violations worldwide. It is a silent, highly organized crime that is difficult to detect, relying on the vulnerability of victims and the manipulation of their identity to facilitate their recruitment, transfer, and exploitation. In this context, biometric technology has established itself as an essential tool to prevent these crimes, accelerate the identification of victims, and support their rescue.
Identity as a key element in human trafficking
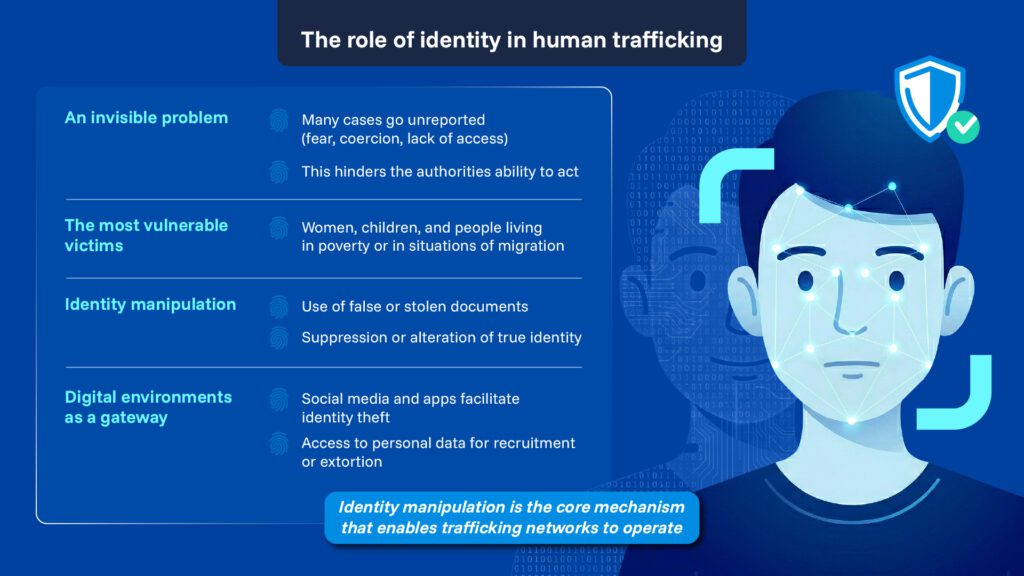
Despite institutional and social efforts, human trafficking remains a largely invisible phenomenon. A significant portion of cases is never formally reported, whether due to fear, coercion, or lack of access to effective protection mechanisms, which consequently hinders the actions of authorities and allows criminal networks to continue operating with relative impunity. In addition, the main victims of trafficking are often women, children, and people in situations of particular vulnerability, which, combined with contexts of poverty or irregular migration, creates a complex environment that criminals exploit.
This is why one of the fundamental pillars sustaining human trafficking is the manipulation of identity. From the first contact to the exploitation phase, criminals systematically resort to the falsification, alteration, or suppression of victims’ identities, as the use of forged documents or documents belonging to third parties allows criminal networks to move victims between cities and even countries, making them difficult to track. Considering this, social networks, dating applications, and other digital environments have become one of the main sources of information for traffickers, as the lack of robust and reliable identity verification processes facilitates impersonation and access to personal data that are later used for recruitment and blackmail.
Biometrics as a new standard of security and protection
Identification systems based exclusively on physical documents are insufficient in the face of increasingly sophisticated criminal organizations. These documents can be stolen, forged, or manipulated with relative ease, especially in contexts of cross-border mobility, making it essential to adopt technologies capable of verifying unequivocally a person’s identity, regardless of the documentation they carry or its location.
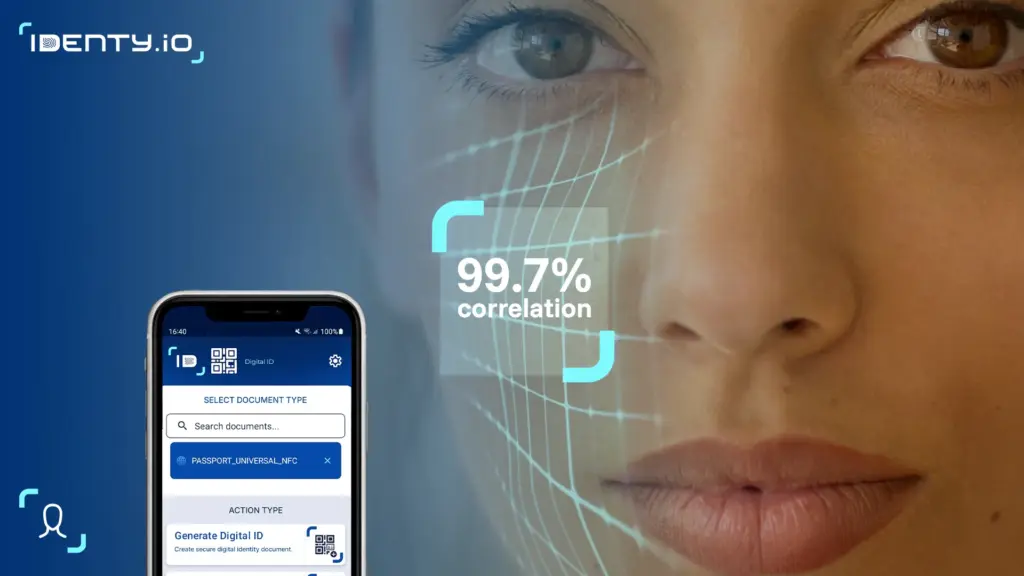
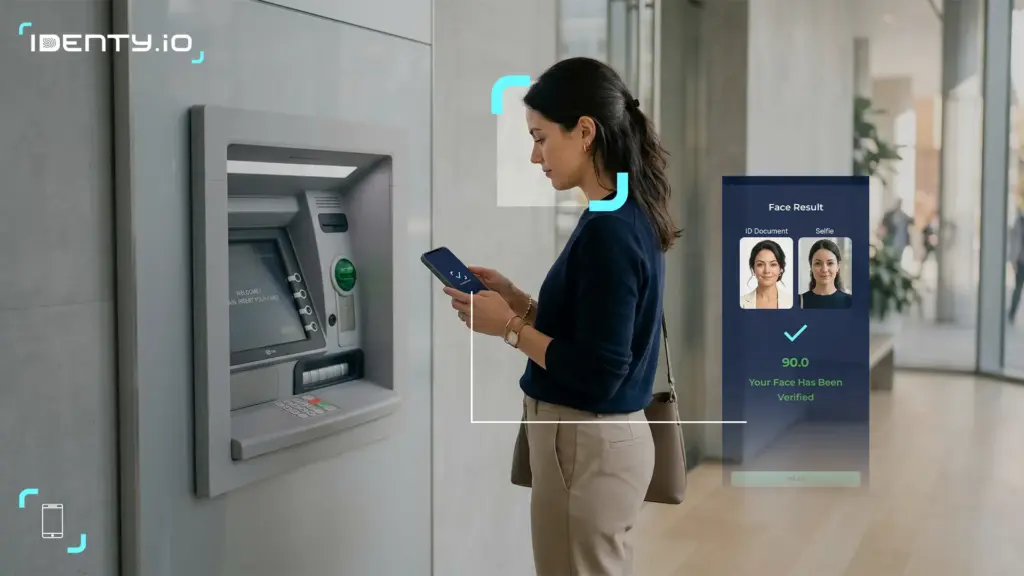
Biometric solutions are based on the capture of unique and immutable physical characteristics (such as fingerprints or facial features) to reliably identify a person. Unlike traditional documents, these credentials cannot be lent, stolen, or easily falsified, positioning biometric authentication solutions as a widely adopted global security standard, with a direct impact on the prevention and detection of crimes such as human trafficking. Thus, the generation of biometric digital credentials provides a reliable identity backup in cases of disappearance or suspected trafficking, as they can be matched within seconds by law enforcement authorities at border controls, airports, banking institutions, or reception centers.
Biometrics does not only act once the crime has already occurred. Its true potential lies in prevention, limiting the recruitment of victims through digital services with robust verification and preventing unauthorized movements in financial or administrative environments. Even when a person has been displaced or their identity has been altered, biometric systems allow for identification during routine checks, generating automatic alerts that accelerate the response of authorities. Thanks to the existence of these biometric databases and the ability to perform reliable real-time matching, it is possible to identify victims even years after their disappearance.
How does Identy.io’s biometric technology help combat human trafficking?
Identy.io has developed biometric identification solutions designed to operate in any context and location, even in environments with technical or connectivity limitations, where the protection of people is most needed.
Advanced biometric capture on-device
Identy.io’s technology allows the capture of all ten fingerprints directly from the user’s mobile phone, without the need for additional devices. Using the phone’s own camera, the system obtains high-resolution biometric images comparable to those captured by traditional readers, ensuring an adequate level of accuracy and enabling a fast and intuitive authentication process by reducing the technical and logistical barriers that typically hinder identity registration, especially in vulnerable or hard-to-reach contexts. This is key to preventing human trafficking. In cases of disappearance, attempted forced transfer, or border crossing, the registered fingerprints can be immediately matched by law enforcement authorities, even if the victim lacks documentation or if it has been falsified.
Passive liveness detection to prevent fraud
Through passive liveness detection, Identy.io’s solution verifies that the biometric capture truly corresponds to a person present at the time of registration, without requiring specific movements or predefined actions from the user. Unlike other more intrusive methods, this approach automatically analyzes multiple biometric and contextual indicators during capture to confirm that it is not an image, a mask, or a deepfake. This capability is essential to prevent the use of digital doubles, forged fingerprints, or silicone replicas, techniques increasingly used by criminal networks to impersonate identities and evade security controls. By ensuring that each biometric record is unequivocally linked to a real, living person, the reliability of the identification process is significantly strengthened.
Local processing and offline operation
All biometric data captured by Identy.io’s solution is processed locally on the device, without the need for an Internet connection, which not only speeds up registration but also allows the technology to operate in remote environments, rural areas, or emergency situations where access to data networks may be limited or nonexistent. This approach ensures that sensitive information never leaves the device until the user decides to share it securely, reinforcing privacy and data protection against unauthorized access. In addition, by eliminating dependence on connectivity, law enforcement authorities can perform immediate matching anytime and anywhere, which is especially critical in the location and rescue of victims.
Interoperability with official systems
Identy.io works with international entities, NGOs, and programs for the protection of minors and vulnerable individuals like The Exodus Road, placing its biometric technology at the service of investigation, prevention, and victim rescue. Through this collaboration, Identy.io provides accessible and reliable tools to law enforcement authorities, facilitating interoperability with official databases and ensuring that biometric records are processed securely and privately. This way, technological collaboration not only strengthens the operational capacity of authorities but also contributes to the prevention and deterrence of trafficking networks, ensuring that the protection of people is faster, more coordinated, and more effective.
Technology with purpose: Identy.io’s commitment
All these technological advances presented by digital identity verification solutions represent a decisive step toward minimizing the impact of these crimes and restoring people’s right to identity.
For Identy.io, technological innovation goes hand in hand with social commitment, which is why its biometric solutions are designed not only to offer the highest level of security but also to protect the most vulnerable individuals and actively contribute to the fight against human trafficking and other crimes where identity is key. Biometrics, always used ethically and responsibly, is consolidated as a fundamental ally in building a safer digital and physical environment, where identity becomes a tool to protect social rights.